Big Data Security Overview
Data security is a concern for all business leaders, but for certain economic sectors it can mean the difference between big profits and devastating losses, good publicity and government scrutiny, or even life and death. CXOs in manufacturing, healthcare, life sciences, retail and finance increasingly value the role of security governance, not merely for developing a disaster recovery plan in the inevitable event of a cyberattack, but as a part of a robust business continuity plan.
The ideal approach to Big Data security allows access to data while maintaining “business as usual” operations, meets regulatory compliance requirements and ensures quality customer service while keeping a company’s cost footprint low and its reputation intact. The best Big Data tools provide data-flow analysis to trace the location of data (and security breaches) at different times during a business process, from the application and service level to the transaction and infrastructure level. Securing Big Data also allows CXOs — including CFOs — to take advantage of the opportunity to mine these datasets for insights and bring the process full-circle by ensuring the security of sensitive information, company operations and company profits going forward.
RoundWorld Big Data 360-degree Tool
 The customizable, template-driven RoundWorld Big Data 360-degree tool can provide a top-level down look at systems and practices while also taking into account the culture and traditions of your institution. RoundWorld can also equip your firm with systems and approaches that maintain compliance and other privacy requirements while also protecting customers’ sensitive personal and financial data.
The customizable, template-driven RoundWorld Big Data 360-degree tool can provide a top-level down look at systems and practices while also taking into account the culture and traditions of your institution. RoundWorld can also equip your firm with systems and approaches that maintain compliance and other privacy requirements while also protecting customers’ sensitive personal and financial data.
Our Big Data 360-degree tool can determine the level of risk at every level of security management, provide a window into how targeted information might be used by cyber criminals in an ever-changing threat environment and help companies act swiftly to determine the nature of an attack and reduce damage should an attack occur.
Our expertise in building robust security practices translates to real, practical solutions for each area within your security scaffolding, from ensuring that customers are educated about how to prevent security breaches to preventing the kind of breaches on an infrastructure level that can hurt both a company’s bottom line and its public trust.
Big Data Security For Life Sciences Sector
In a cyber-threatened world where a single keystroke can mean the difference between data security and certain disaster, the life sciences sector is in particular peril. Although Big Data analytics for data-driven fields like genomics have been championed for bringing about advances in drug discovery and patient care, the deluge of Big Data — including Personally Identifiable Information (PII), Personal Health Information (PHI), and intellectual property — as well as the ease of data sharing means it’s also easier for corporate adversaries to steal sensitive data or use data technologies to inflict harm.
To further complicate matters, the highly sensitive information that life sciences companies manage must be protected while also complying with industry regulations, privacy requirements and state and international laws. This Big Data is often scattered across a multitude of systems, devices and apps, all with their own security protocols and all with the potential to be hacked or otherwise breached.
The risks associated with such sensitive data are an emerging concern for CXOs at every level of management, including CFOs. There is a growing understanding that securing Big Data within the life sciences requires vigilance not for one day or one month, but on a constant and consistent basis. Security breaches can happen anytime, anywhere, and can cost companies billions in fines or loss of assets (not to mention the loss of C-suite careers). For CFOs, the potential loss of trust and harm to a business’s reputation and its stock prices is a risk not worth taking. Even worse, chinks in the life sciences security armor can also have national and transnational repercussions of unimaginable magnitude, ranging from from cyber intrusion to IP theft to the potential development of biological weapons.
Yet to be successfully implemented, data security measures must not compromise a company’s capacity for operating in a globalized economy. On the contrary, an agile, comprehensive approach to data security will actually improve a life sciences company’s ability to navigate health-care reform, deliver innovative, in-demand products, optimize supply chain and comply with regulatory change.
The first line of defense for data security in the life sciences exists at the application level, which represents a growing source of Big Data. Data is now aggregated, collected and sourced by everything from phone apps to pacemakers, which ultimately requires the integration and analysis of multiple datasets that are constantly changing. Specifically in the life sciences, datasets include raw data or heterogeneous data from a multitude of sources, including the health-care system, pharmaceutical industry, the -omics fields (genomics, proteomics, metabolomics, etc) and even agricultural and environmental initiatives.
Unfortunately, the security of these applications and devices is not guaranteed. Data-sharing protections such as encryption, access-control technologies and digital certificates are not always standardized across-the-board and provide increased opportunities for hackers to exploit or steal valuable or sensitive data for financial advantage or to inflict harm.
The life sciences sector must also address security concerns across the service level, primarily in terms of supply chain. Although sharing information with suppliers is crucial, it also presents countless opportunities for data to be stolen, misused or otherwise compromised. According to a 2013 report from the Information Security Forum, 40 percent of the data-security breaches experienced by organizations arise from attacks on their suppliers.
Too many companies, however, fail to properly define risks to data security, especially when the supply chain is extensive. The risk might be understood and managed internally, but when the number of suppliers reaches into the hundreds or even thousands, securing data can become monumentally complex — and expensive. Yet failing to tackle supply chain security can mean the end for businesses that depend on secrecy to remain competitive. Among pharmaceutical companies, for example, the theft of intellectual property in the form of a new drug formula or other trade secrets is a constant looming threat to a company’s relevance and bottom line, and cyber-espionage can happen at any point along the supply chain, even by company insiders.
At the transactional level, life science companies must ensure that their daily transactions — the raw material of business intelligence — do not become the raw material for a cyberattack. Transactional data may come from interactions with customers, management of employees, running of operation or administration of finance, and for the life sciences sector in particular, can represent information of extreme sensitivity. The security of the databases used to record these transactions is therefore of paramount importance, and yet often these databases are distributed throughout the globe and subject to varying degrees of security regulation.
Also important for data security within the life sciences is an understanding of threats at the level of infrastructure. More and more, companies are discovering the importance of ensuring proven security capabilities of all components of their data architectures prior to selection and integration. Changing government regulations for data security, however, make it increasingly difficult to store, manage and protect irreplaceable scientific and patient data while still retaining access to core scientific information, maintaining interoperability and scaling operational infrastructure as needed.
Leveraging the years of learning that security experts have already accomplished in other sectors is critical to the success of life sciences companies who seek to secure their own systems. RoundWorld Solutions’ Big Data 360-degree Tool is designed to provide a detailed look, from the top down, at your firm’s data landscape to create an effective, robust and holistic big data management strategy.
We can help you make mobile access more secure without unduly limiting its usefulness, create a dashboard view of constantly shifting active cybersecurity threats, and help you build an enterprise-wide view of who has access to what within the supply chain. We will work with you to enable the real-time visibility you need to effectively manage your data, mitigate risk and remain globally competitive.
Big Data Security For Healthcare Sector
Most people consider hospitals and healthcare facilities to be places of healing, yet increasingly they are targets for large-scale attacks.
According to data protection group The Ponemon Institute, criminal cyber-attacks are now more likely to occur in the healthcare industry than in any other economic sector. Big Data security breaches at hospitals and other care providers are up 125 percent since 2010. The largest data breach on record took place in in 2015 at Anthem, Inc. (parent company of Anthem Blue Cross, Anthem Blue Shield and other brands), which disclosed that hackers had stolen more than 78.8 million records containing personally identifiable information. Anthem’s shares dropped following the security breach, while tech stocks — tellingly — soared.
These and other nightmare scenarios have transformed many healthcare CXOs’ perspectives on Big Data analytics and data security from the cost-dependent “someday maybe” category to the “must have now at any cost” category. A case could be made, after all, that healthcare data is heavily attacked precisely because security has been so severely underfunded. Firewalls are now becoming as important to hospital operations (and hospital budgets) as new imaging technologies.
But even within the healthcare industry, data projects aren’t solely about mitigating threats to patient privacy. More and more, business leaders are turning to data analytics as a way to increase revenue, growth and advancement. Ensuring that their company’s data remains secure isn’t just good for peace of mind. It’s good for the bottom line. Big Data affords CXOs an opportunity to potentially leverage year-over-year financial data, recover assets and spot trends (in patient behavior or hospital readmissions, for example) that they’re often too preoccupied to notice. In fact, a study published in Health Information Science & Systems found that big data analytics can enable the United States healthcare industry to save more than $300 billion per year.
Nevertheless, the sheer volume of data in terms of complexity, diversity and timeliness can be mind-boggling, and traditional security solutions cannot be directly applied to large and inherently diverse datasets. Within healthcare, it’s not just the sensitive physical and psychological data of patients at the application level (via electronic health records, for example) that pose a security risk.
The Big Data healthcare cloud also includes clinical, financial and social data, not to mention the personal data of physicians and other staff. This poses additional risks at the transactional level, given that fetching data might entail accessing databases kept in entirely different facilities. Genetic data is increasingly available due to advances in genomic research, and such data — which opens the door to healthcare fraud and discrimination suits — could do far more damage if it falls into the wrong hands than a social security number or credit card information.
With the emerging Internet of Things, continuous, real-time patient monitoring devices such as pacemakers — as well as CAT scan machines and refrigerators for storing blood and pharmaceuticals — all have IP addresses that pose a potential lure for hackers. Many of these devices also require software that needs to be updated, making them vulnerable to viruses and other cyber threats. Increasingly, personal health data devices like FitBits and other trackers are being used by physicians for patient care, posing an additional risk at the service level.
Furthermore, the complicated rules related to the Affordable Care Act, proper data governance, and HIPPA compliance mean that it’s difficult for CXOs to ascertain — much less ensure — the security of Big Data assets at an infrastructure level, given those assets are often kept in multiple locations, even competing hospitals, with varying levels of security. In other words, although HIPAA protects patient data, it also makes that data more difficult to analyze in order to spot attacks, improve outcomes, reduce security costs and increase revenue.
Unfortunately, the sheer scale of data being generated means that many organizations wait until after an attack to increase security, which can interrupt daily hospital operations and potentially jeopardize patient care. Care providers, after all, must be able to access data in real-time as securely and as quickly as possible. Big Data security measures that neglect to take into account the needs of hospitals and practitioners could actually create potentially life-threatening problems in the name of securing information. Furthermore, the e-discovery process — an attempt to trace a problem with patient care back to its data source — requires that investigators be provided access to certain datasets collected over time.
Although basic steps can be taken to assess a cyber-threat and develop a proactive response, healthcare leaders must develop more sophisticated tools to both assess risk and determine the investment required to deter and cope with such attacks.
RoundWorld Solutions can assist healthcare providers in aligning patient care, provider needs and business interests with robust security governance. By utilizing the RoundWorld Solutions (RWS) Big Data 360-degree view tool, healthcare organizations can develop a full disaster recovery/business continuity plan that allows access to data, ensures quality patient care and maintains cost benefits and savings.
Our Big Data 360 tool provides CXOs with a unified, top-down view of programs and initiatives that pertain to data security at every level, from applications to services to transactions and infrastructure. Our expertise in building robust security practices translates to real, practical solutions for each area within your security scaffolding, from customizing our template-driven checklist to ensure that documents being shared between hospitals are protected from security breaches to preventing the kind of breaches at a service level that can hurt both a company’s share prices and its reputation. Most importantly, RoundWorld can equip your business with systems and approaches that maintain security and both the transactional and infrastructure levels without jeopardizing clinical operations or patient health.
Data security is a concern for all business leaders, but for those in the healthcare industry, it can mean the difference between life and death. RoundWorld Solutions can help business leaders not only protect their data, but turn that data into actionable insight that can aid patients, create loyalty and promote growth.
Big Data Security For Manufacturing Sector
Over the past decade, Big Data has proven to be an invaluable resource for streamlining and optimizing global manufacturing operations in a variety of industries. Big Data analytics such as distribution histograms, standard deviations and other metrics make it possible for CXOs and operations managers to aggregate a pipeline of data — even real-time data — from the shop floor to the warehouse and throughout the supply chain. By taking a comprehensive look at previously isolated datasets, industry leaders can dive deep into current and historical production processes, pinpoint complex patterns and guideposts, reduce waste and variability and optimize yield, quality control and lean manufacturing on the whole.
Big Data, therefore, isn’t just the domain of manufacturing CIOs. More and more CFOs are taking notice of the power of Big Data to cut costs, increase productivity and turn a bigger profit for shareholders, while simultaneously increasing brand-name recognition and building customer loyalty. Given their responsibility for maintaining control over financial reporting and planning for the future, manufacturing CFOs must also be able to track information across all sectors of the supply chain, from inventory to distribution centers, even when the supply chain is scattered across multiple floors in multiple factories on multiple continents.
And yet anywhere there is data, there are thieves trying to steal or otherwise compromise that data. Although security threats vary depending on what products a company makes, intellectual property and trade secrets will always be a source of temptation for hackers and other cyber criminals. Given the ever-increasing shrewdness and temerity of cyber-criminals, manufacturers should not just prepare for but expect to be targets.
Indeed, the Global State of Information Security Survey of 2015 found that three quarters of industrial manufacturing companies had detected security incidents over the past 12 months, and about 20% said they detected 50 or more such incidents. Stolen, damaged or otherwise compromised were employee records, personally identifiable information about customers or partners, internal records and soft intellectual property such as processes and institutional knowledge. Nearly 40 percent of those manufacturers attributed current or former employees as the likely source of the breach.
Complicating matters is the sheer number and complexity of global manufacturing operations, which often creates a fragmented data landscape that is difficult to secure. The same Industry trends that make manufacturing more streamlined — such as the Internet of Things (IoT) and Bring Your Own Device (BYOD) — also increase exponentially the potential for cyber attacks to occur.
“Schneider is a 200,000-person global company spread out across the globe and made up of regional environments that are like companies within themselves,” says Mark Zecca, CIO and Senior Vice President for Cloud Services and Engineering for Kyriba and formerly the senior director for business systems at Schneider Electric. “The data comes from multiple data marts inside the company, all these nooks and crannies from the company’s local environments. One of our first security concerns is that the data originates from all sorts of semi-known sources. The question is: What is coming in with it and what is it going to transmit as we make it part of our data stack? That’s how your data is consumed so you don’t propagate everything from viruses to worms that can come in with the data.”
Cyber attacks, whether through cyber espionage or distributed denial of service (DDOS) and Web application attacks, can wreak havoc on a manufacturing company’s reputation, operations and bottom line, not to mention the consequences that arise if equipment is compromised and employees’ lives are put at risk. If the breach is severe enough, a company might never regain losses — a fate made all the more painful if the fault lies with the manufacturer itself for not taking appropriate data security measures.
At the application level, any company with a notable online presence is vulnerable to a security breach. Hackers often go after a company’s website or applications with denial-of-service attacks, which can greatly impact operations throughout the supply chain. According to the IBM X-Force Threat Intelligence report, these attacks were second in frequency only to SQL injection, and in some cases they are even politically motivated. Manufacturing, unlike banking or other sectors, wouldn’t seem to be a natural target for politically motivated cyber attacks, but the recent experience of several agricultural equipment manufacturers proves otherwise. The manufacturers — one of which made logging equipment and another weaponized bulldozers used by resettlement operations in the Middle East — demonstrate that nearly any company can find itself under attack by not only those looking to make fast money, but also those looking to prove a point.
Information is the glue that holds a supply chain together, but at the service level of manufacturing, the supply chain is often the the weak point for attacks. Protecting information exchanged with suppliers is a huge challenge for most manufacturers, which often don’t know exactly who is in their supply chain or even how many suppliers they have. Assessing and managing this information is crucial to securing data, especially given that some suppliers are also competitors. It’s also important for another reason: hackers are increasingly taking advantage of gaps in supply chain security to target manufacturers’ products themselves. Cyber criminals have been known to install Trojans into a product’s control software or even target intelligent devices spread throughout the shop floor — devices that capture valuable company data or, in the event they malfunction, can pose a risk to employee or customer safety.
Cyber attacks can also affect manufacturing operations on a transactional level. The real-time or near real-time transaction processes in typical Industrial Control Systems — fetching information about current inventory, for example — affords little tolerance for long periods where services are unavailable. However, security controls and solutions for preventing such transactional latency must often be tested off-line in a non-production environment, which is not ideal for either data defense or manufacturing operations.
Furthermore, security components designed to protect data transactions are routinely neglected for years or even decades, causing them to be outdated and vulnerable to attack. These breaches are sometimes not detected for months, which can compromise a company’s financial bottom line. One rule of thumb that many industries have learned the hard way is that the longer it takes a company to discover a security breach, the greater the loss in data and the greater the costs associated with fixing the problem and making things right.
At the level of infrastructure, legacy equipment is often a primary target for hackers. An ever-growing number of corporate assets and products are now linked via IoT, which provides a rich source of data for manufacturers in terms of remote asset tracking, fleet management and performance monitoring, among other data, but also presents an irresistible temptation for those with bad intentions. Security must therefore be addressed not only in security networks, but also in industrial automation systems, sensors and other technologies used to track and monitor products and machines, and devices in the field.
Adds Zecca: “A second security concern is about the content of data itself and its exposure; you can have data that might be relevant in one country but could be considered antitrust in another. You have to be able to catalog the content so you know that you don’t have content that could be illegal or dangerous to the business environment. We do this by using different catalog engines that are a part of the data library system. We tag the metadata using a metadata table to create metadata filtering process. This creates a warning system for content that could be dangerous, whether it’s a regulation or compliance issue.”
Although security systems provide needed protection, they , by their nature, require various layers of access. Access can be maintained, says Zecca, through a series of multilevel profiles.
“A business analyst in the USA, for example, might have general access to a business infrastructure claim, but within that access are a series of permissions,” he explained. “Those permissions allow you to get to catalog stacks identified by metadata, certain sandboxes or certain data marts. Within those datamart, you might have permissions to do EPLs from the main data warehouse. A company has to maintain this with a series of approvals, similar to any other system that creates a multilevel or passage environment. There has to be a guy with a skeleton key who controls it all.”
Big Data Security For Retail Sector
For years, retail executives have mined economic trends, demographic profiles, purchasing histories and other Big Data to develop powerful marketing tools for increasing revenue. But following a barrage of high-profile cyber-attacks on Target, Adobe Systems, Home Depot, Ashley Madison and countless other retail companies, CXOs are increasingly shifting their focus from treating Big Data as a source not only of rich financial insight but one of potentially catastrophic risk.
Despite a decade or more of effort and spending in the billion-dollar range, the global retail industry remains inadequately protected against data thievery and malicious attacks on the sensitive financial and personally identifiable information on which it depends. Of the 970 financial professionals who responded to a survey at the Association for Finance Professionals conference in 2013, 62% said that their organization has been subject to either an actual or attempted cyber-attack at least once over the past year — and those are just the known attacks. Some attacks aren’t discovered until a year or more later, at which point the damage can be insurmountable. Not only do these attacks decimate a company’s reputation, they also represent a high financial cost: customers’ credit cards must be replaced, for example, and stock prices often take a significant hit.
Historically, retail CIOs have been charged with addressing data vulnerabilities but CFOs are increasingly playing a crucial role in the important work of security management. According to Deloitte’s third-quarter 2014 CFO Signals™ report, 74% of the 103 CFOs surveyed said cyber-security is a top priority, while only 6% deemed it a lower priority. Retail CFOs, for one, are responsible for maintaining control over financial reporting, and must understand where information is at all times — and how it is secured — to prevent loss of funds through theft or the cascading effect of a business partner’s security breach. CFOs are also expected, of course, to provide complete disclosure to their corporate board, including disclosure about the possibility of cyber-attack and its potential effect on the financial standing of the company.
The most common threat vector associated with the retail industry is theft of credit card information at the application and transactional levels (via online or in-store shopping, for example), but risks also exist at the levels of both service (especially in terms of supply chain) and infrastructure, which is increasingly controlled by cloud computing and distributed servers at multiple stores across multiple states or countries, scattering sensitive customer data far and wide.
With the booming popularity of online shopping and shopping apps, Big Data security at the application level is of paramount importance. Although these websites and apps make shopping simple and convenient, they can also jeopardize customer data when data-sharing protections such as encryption, access-control technologies and digital certificates are not adequately robust or standardized across-the-board. Moreover, end users are too often tricked through hackers’ social engineering efforts into accessing malware-laden websites, downloading infected files or using weak passwords that can compromise not just their data, but the data of millions of others.
Retail transactions have always been a target for thieves, and transactional-level attacks continue to represent perhaps the greatest source of headaches for CXOs in this sector. Complicating matters within the contemporary retail ecosystem is the inclusion of third-party financial institutions. Attacks on targets such as banks and companies like PayPal can adversely affect business when customers no longer feel that using their credit card, debit card or online account is safe. Security must also be ensured at point-of-sale terminals such as cash registers, barcode scanners credit-card swipe machines equipped with PIN pads, which are too often the target of PIN thefts.
Service-level attacks, while not as common as those at the transactional level, still represent a significant threat to Big Data security for retail. IBM Security Intelligence reports that attacks by those with intimate knowledge of retail companies account for only 3 percent of data security breaches, but the fallout can be monumental. Moreover, when a culture of security is not established within a company, a service-level breach at one checkpoint within a company can lead to a domino effect. Supply-chain data breaches also represent a growing threat within the retail sector, especially with continued reliance on outsourcing and manufacturing in the developing world, where security protocols might not be as robust.
At the infrastructure level, retail companies have seen a surge of distributed denial-of-service (DDoS) attacks, an attempt by multiple servers to send simultaneous requests to the target’s Web servers with the intent of making them crash. When a retail website crashes, its customers go elsewhere. Even worse, attackers often use DDoS attacks to distract a company while they simultaneously steal customer data. Compounding the problem is a sector-wide dependence on legacy or unpatched technologies. Insecure system configurations can also facilitate or exacerbate these attacks, and companies must also increasingly consider the safety of IoT-based devices such as printers and security cameras. Even wireless access or the in-store voice or IP network can pose a security hazard when malicious hackers can gain access.
Yet for all the security risks attributed to Big Data, retail companies’ confidential data files — such as internal emails and audio recordings of telephone conversations — also provide a means to manage that risk. One example that can provide Big Data security at the service level is a technology called “natural language processing,” which mines millions of documents — such as transcripts of phone calls — to reveal the word order and tone of telemarketers as they attempt to sell a particular product. This insight could help a bank’s risk managers, for example, avoid unwanted attention from regulators by either firing or retraining call-center workers who are engaging in predatory lending practices.
The cost of a cyber-attack, whether financial or reputational, can be astounding. As cyber-attackers become more organized and their attacks more sophisticated, industry executives must take action to shore up security protections and protect their company’s brand reputation, trust dynamic and financial bottom line. Finance chiefs understand that spending a small amount up front can not only save the organization a great deal in the event a breach occurs, but — when Big Data is managed wisely and securely — can provide a significant return on investment in peace of mind.
Big Data Security for Finance Sector
The bank robbers of the past used guns and getaway cars to commit crime, but modern-day bank robbers have at their disposal a tool far more capable of inflicting widespread damage: Computers. And although criminals are, to be sure, still after the money, now they’re also after something arguably as valuable: Big Data.
As the release of the so-called Panama Papers recently demonstrated, financial institutions are top targets for those seeking to leak or otherwise compromise sensitive data, be it for politically-driven public shaming campaigns or financial gain. While it’s true that all business sectors are vulnerable to attacks by cyber-criminals, security breaches at financial firms tend to wreak the most havoc in terms of media attention and governmental inquiries, given the public’s expectation that these institutions represent the “safest of the safe” when it comes to data security.
But for banks and other financial firms, safeguarding financial data from security breaches is as complex an endeavor as it is crucial. The data itself is highly diverse, ranging from customer financials and account information to cardholder data, transactions and non-public personal information. Banking and financial institutions also need to secure the storage, transit and use of this sensitive data across business applications, including online banking and electronic communications. Furthemore, almost all the Big Data generated or used by banking and financial services is formally regulated, whether by PCI-DSS requirements for credit card information or even the U.S. Patriot Act.
Although these large, consolidated datasets can provide enormous strategic and competitive value for CFOs looking to enter into new markets or offer new financial products, they also provide a tempting target for cyber criminals. Financial institutions must continually balance their need to secure this data to ensure minimum risk while also maximizing return — a reality that highlights the need for CFOs, and not just CTOs, to take an interest in the protection of Big Data.
Complicating matters is the nature of the typical finance IT environment, which mixes new and legacy systems and applications across vast networks of branch offices, call centers and web portals. The increasingly global nature of the financial services industry makes it necessary to comprehensively address international data security and privacy regulations. Security solutions are often put in place at points along the way, but many of the traditional checkpoint security solutions that are deployed increase both management costs and complexity, and leave gaps between systems and applications that are highly vulnerable to attack.
At the application level, for instance, firms in the finance sector must contend with the weakest link in the security chain: Users and their devices. In a 2012 attack dubbed “Eurograbber,” cyber criminals in Europe stole upwards of 36 million Euros from corporate and personal bank accounts by first tricking customers into installing malware on their PCs and then their mobile phones. The hackers subsequently bypassed the banks’ two-factor authentication and used the corresponding transaction authentication number (TAN), to make transfers of between 500 and 250,000 Euros from the victims’ accounts, meanwhile gaining access to the customers’ sensitive personal and financial information. This scenario, and others like it, underscores the importance of reminding finance customers to be vigilant about ensuring their computers and other devices are equipped with all possible security layers, and ensuring that security software is kept up-to-date.
Service level attacks on financial firms often come in the form of a so-called “drive-by download attack,” in which a hacker, posing as a bank’s customer service representative, sends an email or otherwise tricks a customer into visiting a website that has been compromised and designed to look identical or very similar to legitimate banking websites. The user’s computer is then infected with unwanted — and invisible — software that exploits exposed security flaws in the user’s web browser and operating system. Once the hacker gains control of the user’s computer and turns it into a zombie or ‘bot, the hacker then has access to all manner of personal or financial information. These stealth attacks are difficult to prevent because, like application level attacks, they also require educating users about possible threats and directing them to online “blacklists” of malicious users.
The recently discovered Metel crimeware package provides some insight into the growing level of threat to banks and other financial firms at the transactional level. Metel hackers usually infect banking systems from within by exploiting vulnerabilities in web browsers or by tricking employees into execute malicious files attached to spear-phishing emails. The criminals then burrow further into the network by using legitimate security and administrative software to compromise other PCs and ultimately try to gain control over PCs used by call center operators or IT support, which typically have access to money transactions and sensitive data. These types of attacks are a threat to both data security and a firm’s bottom line. One of Metel’s most powerful components allowed criminals to withdraw nearly unlimited sums of money from ATMs belonging to another bank and then repeatedly resetting their card balances and bypassing the threshold that would normally freeze the card. In 2015, a bank in Russia lost millions of rubles in a single night after being attacked by Metel. Two other groups of cyber criminals — GCMan and Carbanak — also used spear-phishing to target dozens of banking and other financial systems directly by worming their way inside their networks and “spying” on the firm’s’ transactions and other business dealings from afar, providing them a direct window into the firm’s’ Big Data holdings.
From an infrastructure standpoint, the growing threat associated with rootkits and other malicious infiltrations of code means that financial institutions must consider security from the level of the file system to the database and beyond, while still allowing for common policy control and management infrastructure of both data-in-use and data-at-rest.. A robust and yet efficient system for safeguarding data requires that a bank or firm’s big-data initiatives — as well as traditional data centers, virtual environments, or cloud infrastructure — is supported by common policy control and agents to ensure there are no gaps in security or Achilles’ heels in terms of data protection.
As the software platforms supporting Big Data move to mainstream use within the finance sector, managing data security — while also maintaining access to the data where needed — requires continuous diagnostics and monitoring. Data security is a concern for all business leaders, but for those in the finance industry, breaches can have a profound effect on public trust and the global economy as a whole.
RoundWorld Solutions Big Data Security Case Studies
RoundWorld Solutions (RWS) and its business partners have participated in several BI projects involving data consolidation, systems migration, database scrubbing, and several other ETL projects. RWS team brings in a wealth of knowledge and experience when it comes to providing creative solutions to the most challenging data problems. The goal of all Business Intelligence and Data Analytics project is to provide the business with the most appropriate information as and when needed to create value for the enterprise and delight the customers.
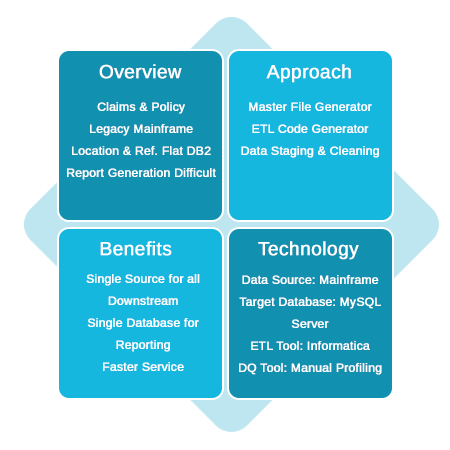
Case Study: Insurance Services
This project involved integrating and migrating data from several sources and legacy systems with inordinate delay in report generation and cycle time to the customer. After the Business Intelligence and Data Warehousing strategy was adopted the service and cycle time have improved significantly with tangible benefits.
Case Study: Financial Services
This project involved providing senior management with Management Decision Support (MDS) system created by extracting important performance data from Management Information System (MIS). The aim was to provide timely and accurate information on business, customer and revenue information.
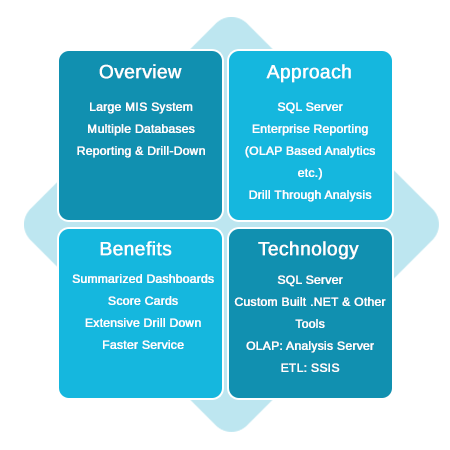
The financial organization had several benefits including extensive what if scenario analysis and other KPI measures that were valuable in product strategy and customer service domains.

